Update on yesterday’s post.
Spoken with several CorVel customers today and late yesterday; all spoke well of CorVel’s response and communications about the systems issue.
Still haven’t’ seen a public statement.
I’ve been told by multiple sources that CorVel’s systems problems appear to be due to the Ryuk ransomware worm; workers in at least two CorVel offices were recently informed of the worm. This worm is linked to attacks on several cities as well, including Stuart FL.
According to CrowdStrike, the worm has been attributed to:
GRIM SPIDER, a sophisticated eCrime group that has been using the Ryuk ransomware since August 2018, targeting large organizations for a high-ransom return. This methodology known as “big game hunting” signals a shift in operations for WIZARD SPIDER, a criminal enterprise of which GRIM SPIDER appears to be a cell. The WIZARD SPIDER threat group, known as the Russia-based operator of the TrickBot banking malware, had focused primarily on wire fraud in the past.
CorVel has been telling customers it hopes to be back up and running Monday (three days from today); on average other Ryuk victims have taken 9 days to recover fully. The company has told customers it discovered the issue early, and this may help reduce the time lag.
In addition to CrowdStrike, companies including Coveware and Malwarebytes advertise services that ostensibly protect systems from Ryuk and other ransomware attacks.
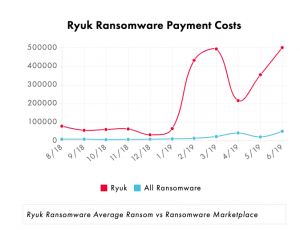
CrowdStrike indicates the worm has been associated with about $3.7 million in ransom payments in recent months; the graph below was developed by Coveware. Please note that there is no indication CorVel has paid or intends to pay the ransom.
Research indicates even those entities that paid the ransomware may have had difficulty restoring files and operations; from Coveware:
Ryuk Ransomware has a low data recovery-success rate after a ransom payment is made. Relative to other types of ransomware, the decryptor tool is very labor intensive and prone to failure.
The worm’s name comes from a character in a Japanese manga novel; he’s not exactly a picture of your kindly uncle…



